Serviciile Onion sunt servicii care pot fi accesate doar prin Tor. Rularea unui serviciu Onion oferă utilizatorilor dvs. toată securitatea HTTPS, cu beneficiile adăugate de confidențialitate ale Tor Browser.
De ce serviciile Onion?
Serviciile Onion oferă utilizatorilor lor diverse avantaje de confidențialitate și securitate.
Ascunderea locației
Adresa IP a unui serviciu Onion este protejată. Serviciile de tip Onion sunt o rețea de suprapunere deasupra TCP/IP, astfel încât, într-un anumit sens, adresele IP nu sunt chiar importante pentru serviciile Onion: nici măcar nu sunt utilizate în protocol.
Autentificare end-to-end
Când un utilizator vizitează un sait printr-un serviciu Onion, furnizorii știu că cererea provine doar de la acel serviciu Onion. Nu este posibilă nici o răspundere, și, în general, nu este cazul. De obicei, accesarea unui site web nu înseamnă că un mijlocitor nu s-a reorientat către o altă locație (de exemplu, atacurile DNS).
Criptare end-to-end
Traficul serviciului Onion este criptat de la client la gazda Onion. Aceasta este ca și cum ați folosi un SSL/HTTPS puternic și gratuit.
punctarea NAT
Rețeaua dvs. este filtrată și nu puteți deschide porturi pe firewall? Acest lucru s-ar putea întâmpla dacă vă aflați într-un campus universitar, un birou, un aeroport sau aproape oriunde. Serviciile Onion nu au nevoie de porturi deschise, deoarece sunt punctate prin NAT. Ele stabilesc doar conexiunile de ieșire.
Protocolul Serviciului Onion: Prezentare generală
Acum, apare întrebarea ce fel de protocol este necesar pentru a atinge toate aceste proprietăți? De obicei, oamenii se conectează la o adresă IP, dar cum vă puteți conecta la ceva care nu are o adresă IP?
În special, adresa unui serviciu Onion arată așa: vww6ybal4bd7szmgncyruucpgfkqahzddi37ktceo3ah7ngmcopnpyyd.onion
Acest lucru pare ciudat și aleatoriu, deoarece este identity public key a serviciului Onion. Acesta este unul dintre motivele pentru care putem realiza proprietățile de securitate de mai sus.
The onion service protocol uses the Tor network so that the client can introduce itself to the service, and then set up a rendezvous point with the service over the Tor network. Iată o detaliere a modului în care se întâmplă acest lucru:
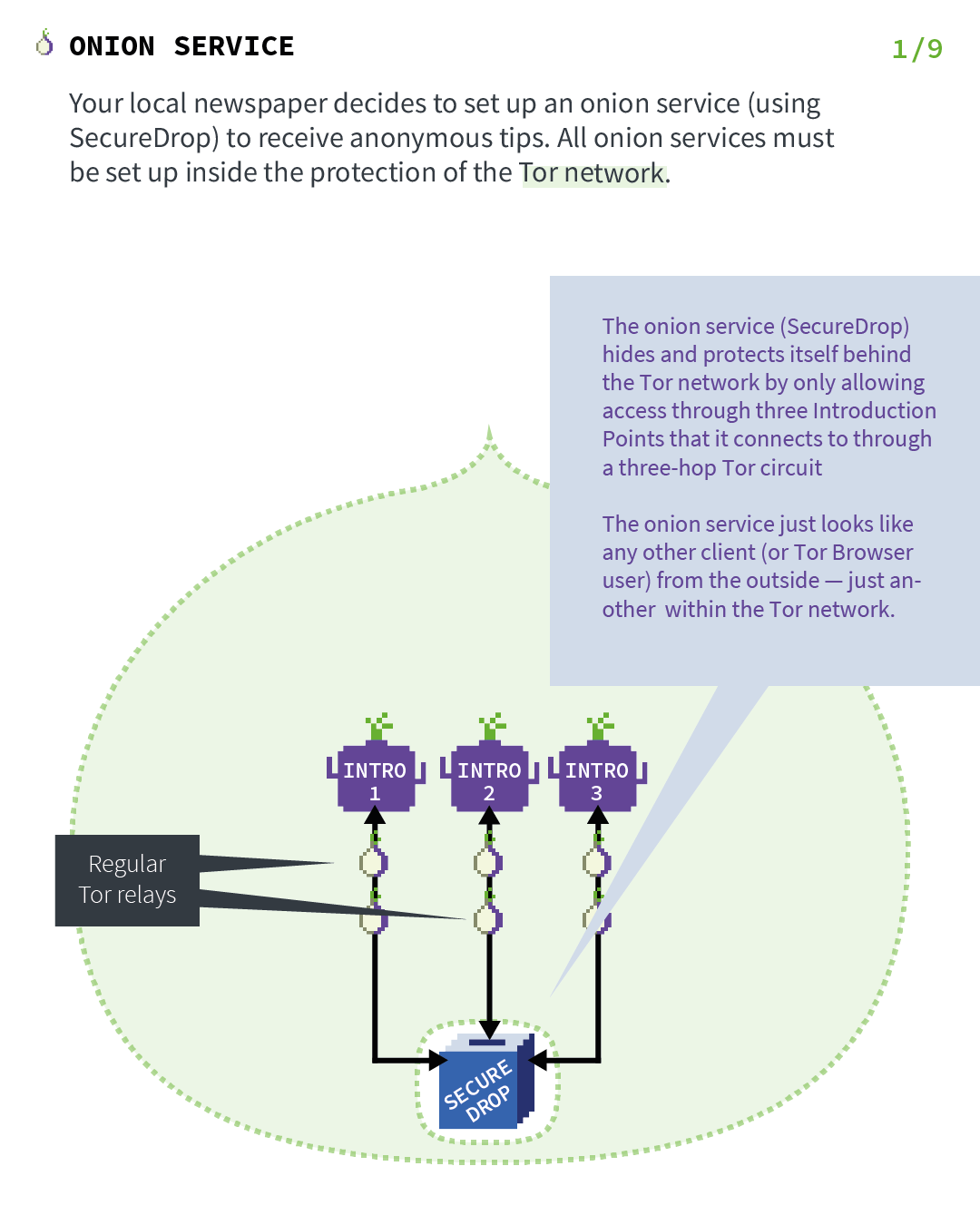
Actul 1: În care serviciul Onion își stabilește punctele de introducere
Let's imagine that your local newspaper decides to set up an onion service (using SecureDrop) to receive anonymous tips. As the first step in the protocol, the onion service will contact a bunch of Tor relays and ask them to act as its introduction points by establishing long-term circuits to them. These circuits are anonymized circuits, so the server does not reveal the service location to the introduction points.
The onion service will hide and protect itself behind the Tor network by only allowing access through three introduction points that it connects to through a two-hop Tor circuit.
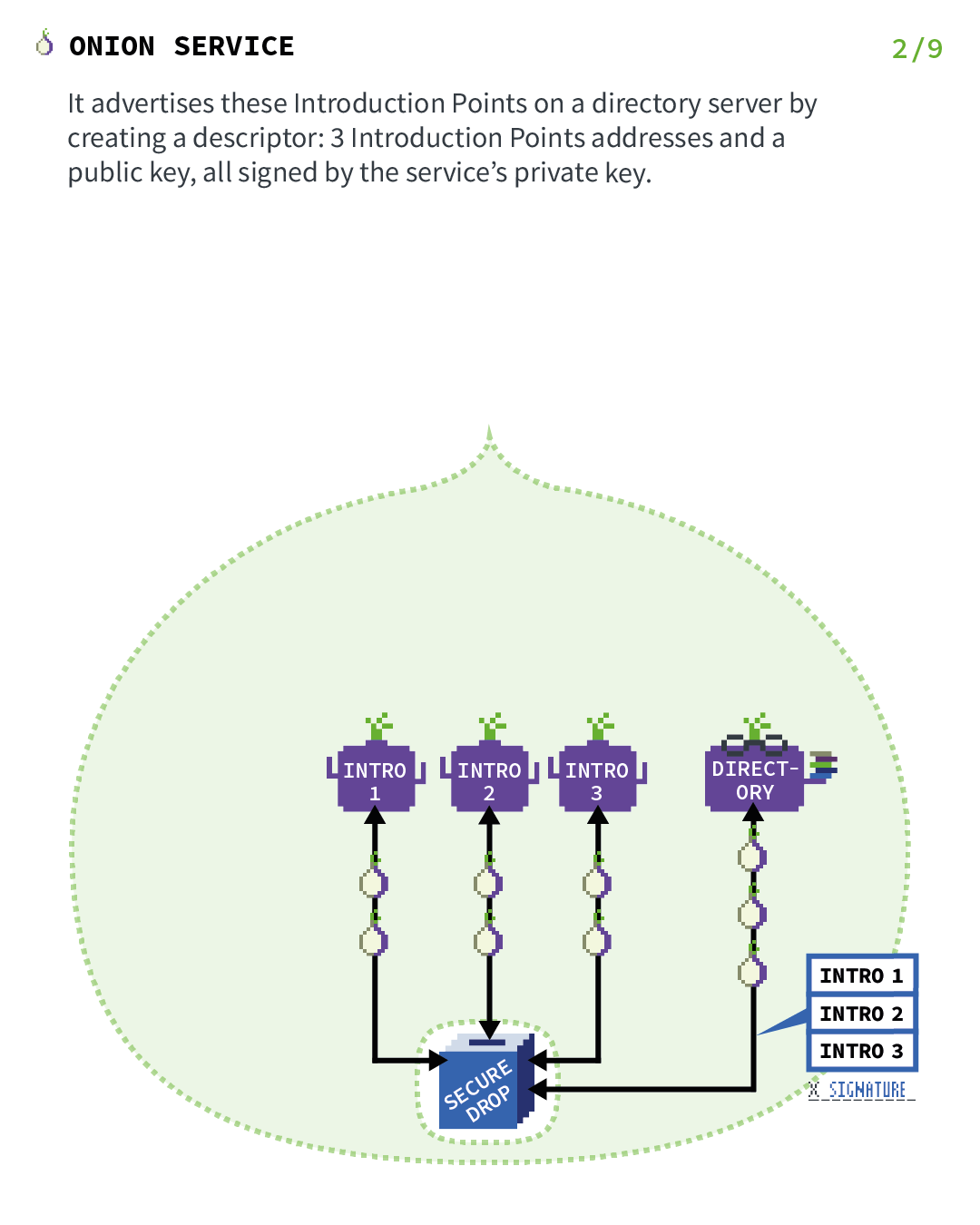
Actul 2: În care serviciul Onion își publică descriptorii
Now that the introduction points are set up, we need to create a way for clients to be able to find them.
For this reason, the onion service assembles an onion service descriptor, containing a list of its introduction points (and "authentication keys"), and signs this descriptor with the onion service's identity private key. Cheia de identitate privată identity private key folosită aici este partea privată a cheii publice care este codată pe adresa serviciului Onion.
The onion service upload that signed descriptor to a distributed hash table, which is part of the Tor network, so that clients can also get it. It uses an anonymized Tor circuit to do this upload so that it does not reveal its location.
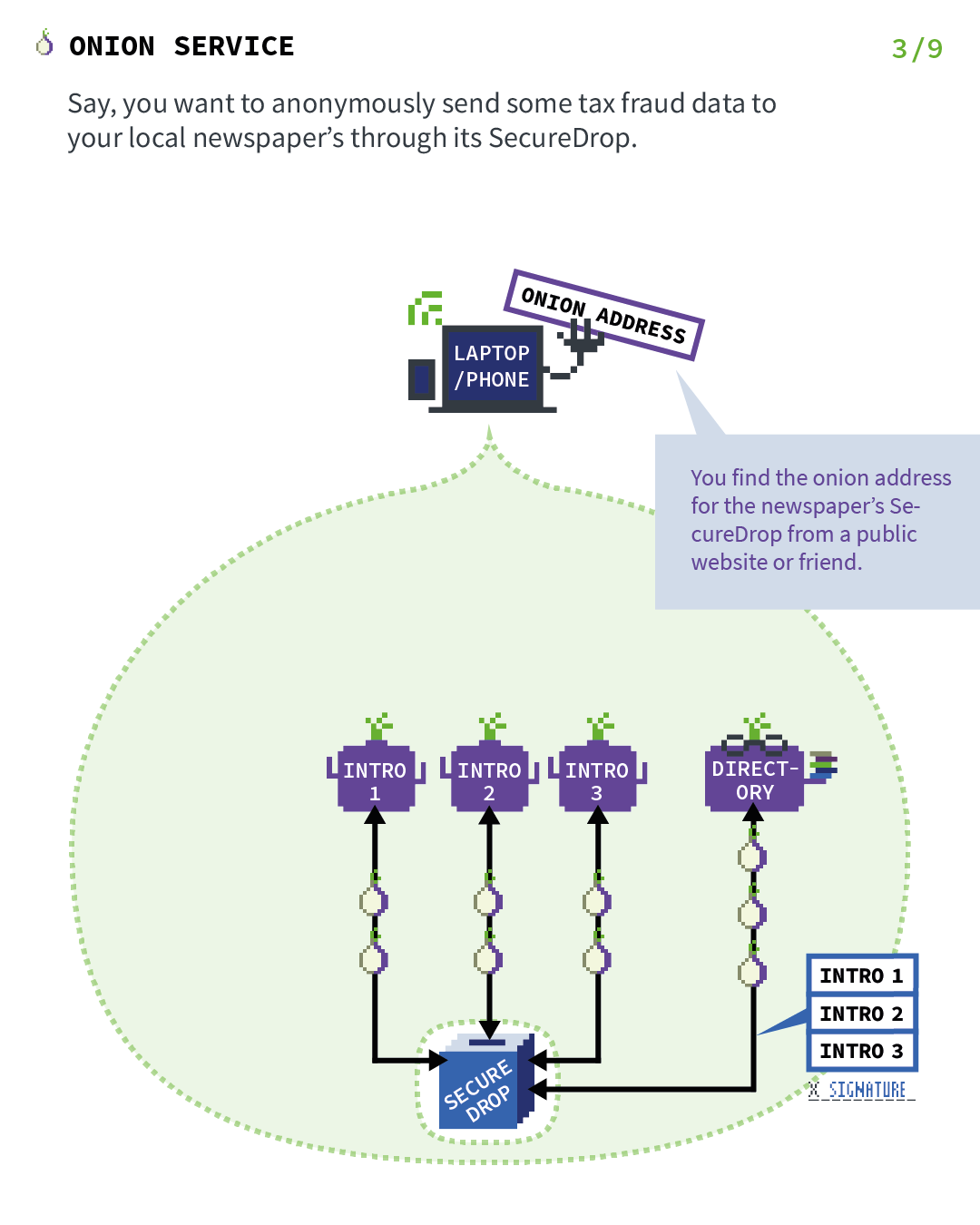
Act 3: Where a client wants to visit the onion service
Say you want to anonymously send some tax fraud data to your local newspaper through its SecureDrop. You find the onion address for the newspaper's SecureDrop from a public website or friend.
Act 4: Where the client introduces itself to the onion service
All the previous steps were just set up for the onion service so that it's reachable by clients. Now let's fast-forward to the point where an actual client wants to visit the service.
In this case, the client has the onion address of SecureDrop and want to visit it, so they connect to the service with Tor Browser. Now the next thing that needs to happen is that the client goes to the distributed hash table from Step 2 and ask for the signed descriptor of SecureDrop's onion service.
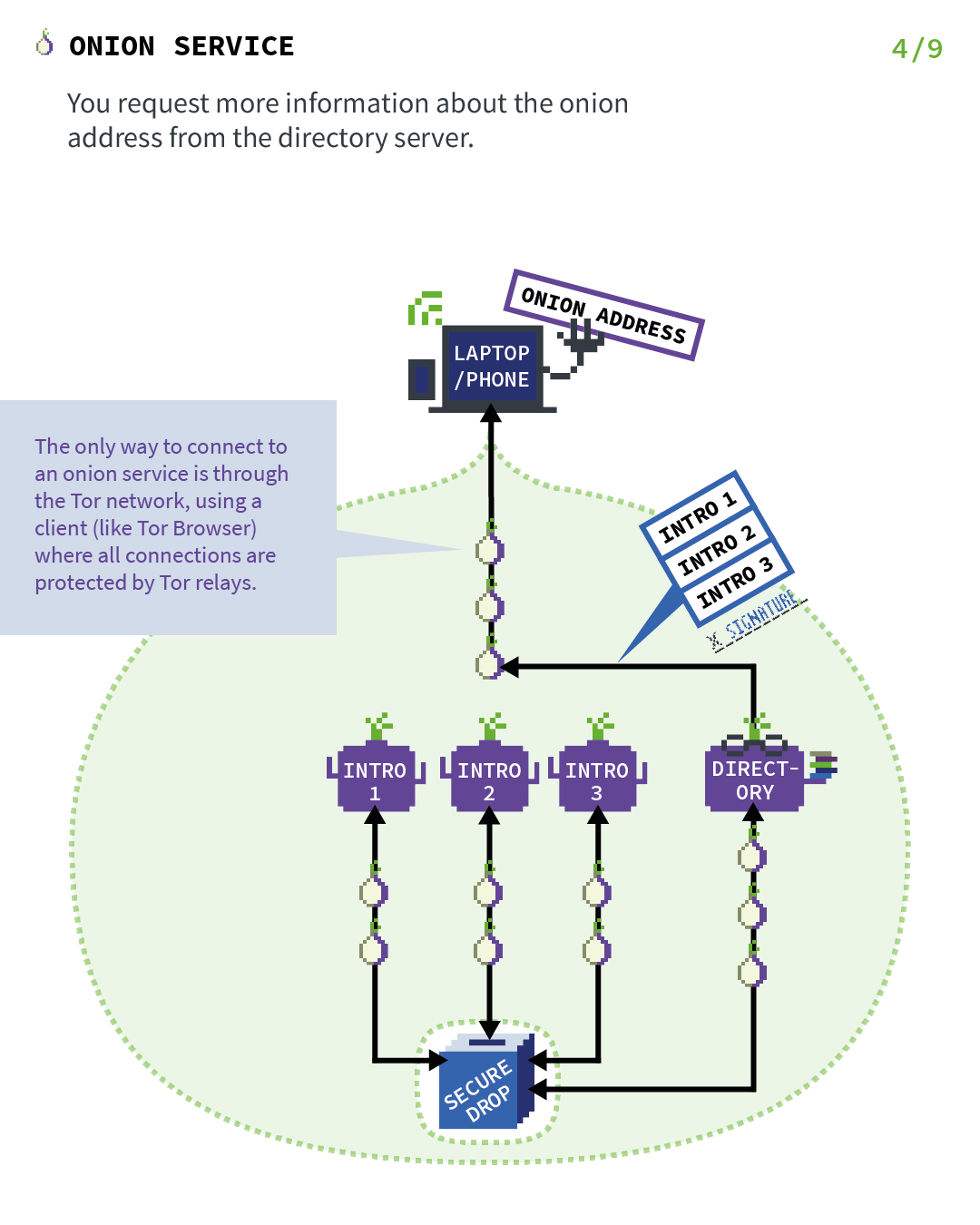
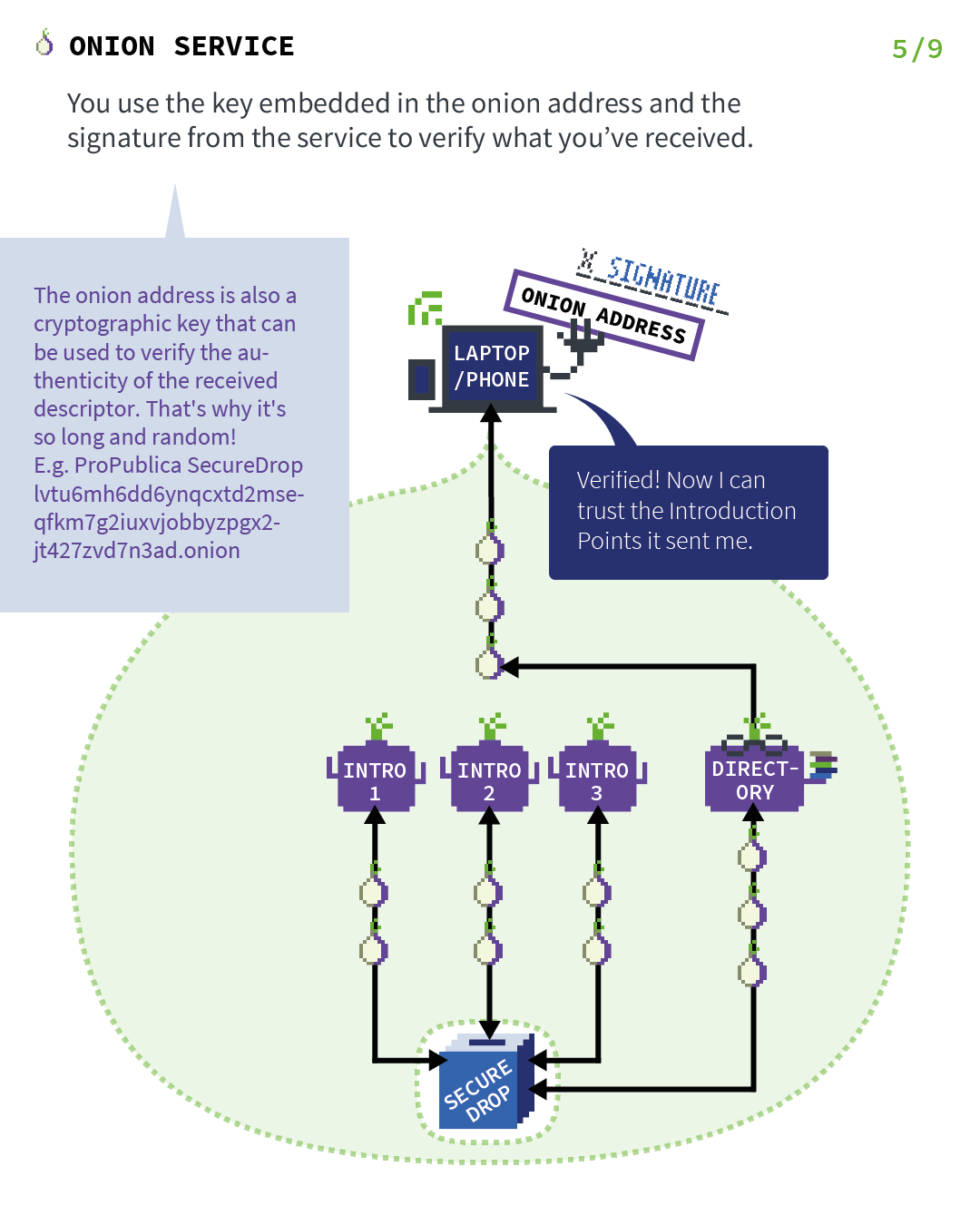
Act 5: Where the client verify onion address signature
When the client receives the signed descriptor, they verify the signature of the descriptor using the public key that is encoded in the onion address. This provides the end-to-end authentication security property, since we are now sure that this descriptor could only be produced by that onion service and no one else.
And inside the descriptor, there are the introduction points that allow the client to introduce themselves to SecureDrop's onion service.
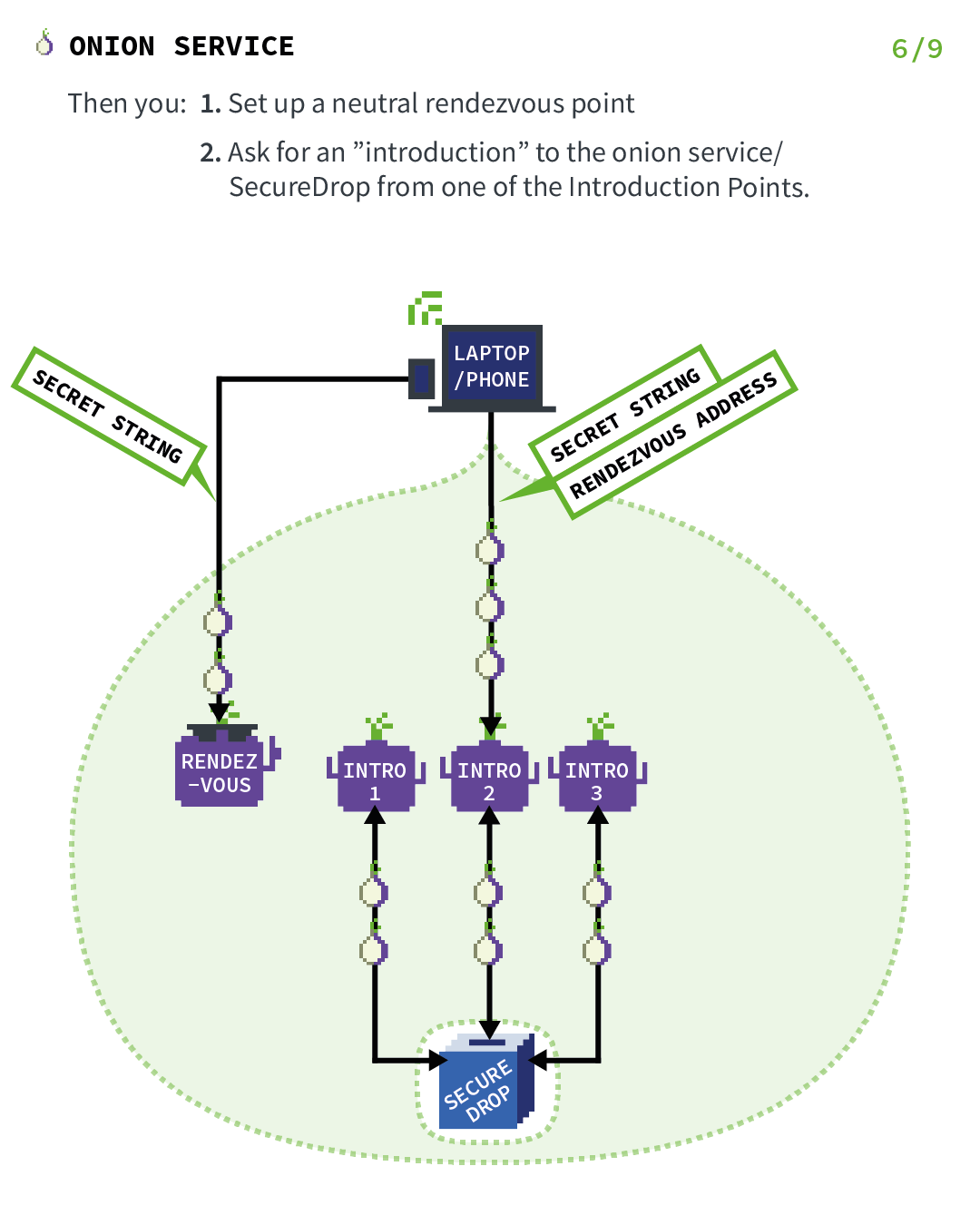
Act 6: Where the client establishes a rendezvous point
Before the introduction takes place, the client (in this case, you) picks a Tor relay and establishes a circuit to it. The client asks the relay to become their rendezvous point and give it an "one-time secret" that will be used as part of the rendezvous procedure.
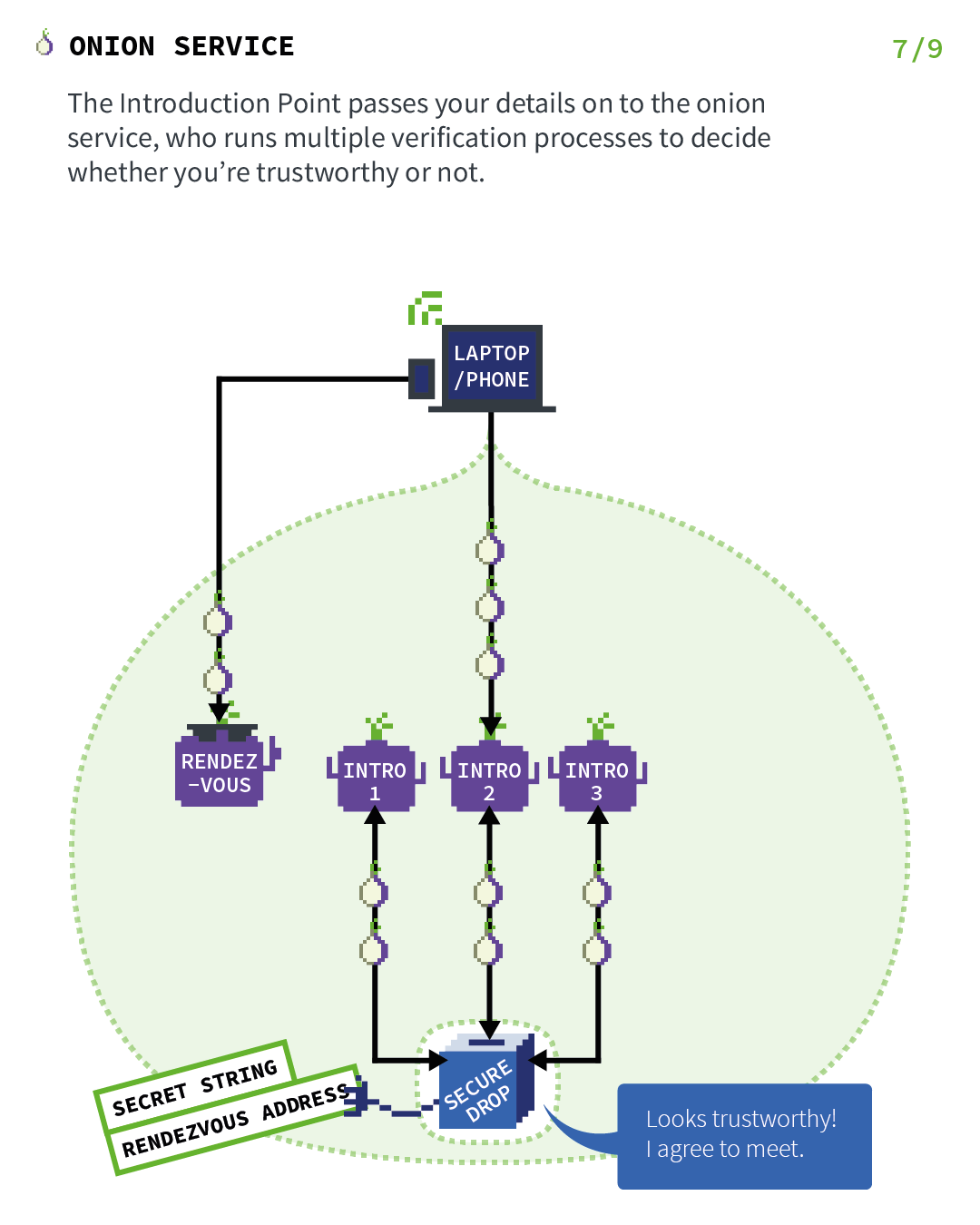
Act 7: Where the onion service rendezvous with the client
The introduction point passes your details (secret string and rendezvous address) on to the onion service, which runs multiple verification processes to decide whether you're trustworthy or not.
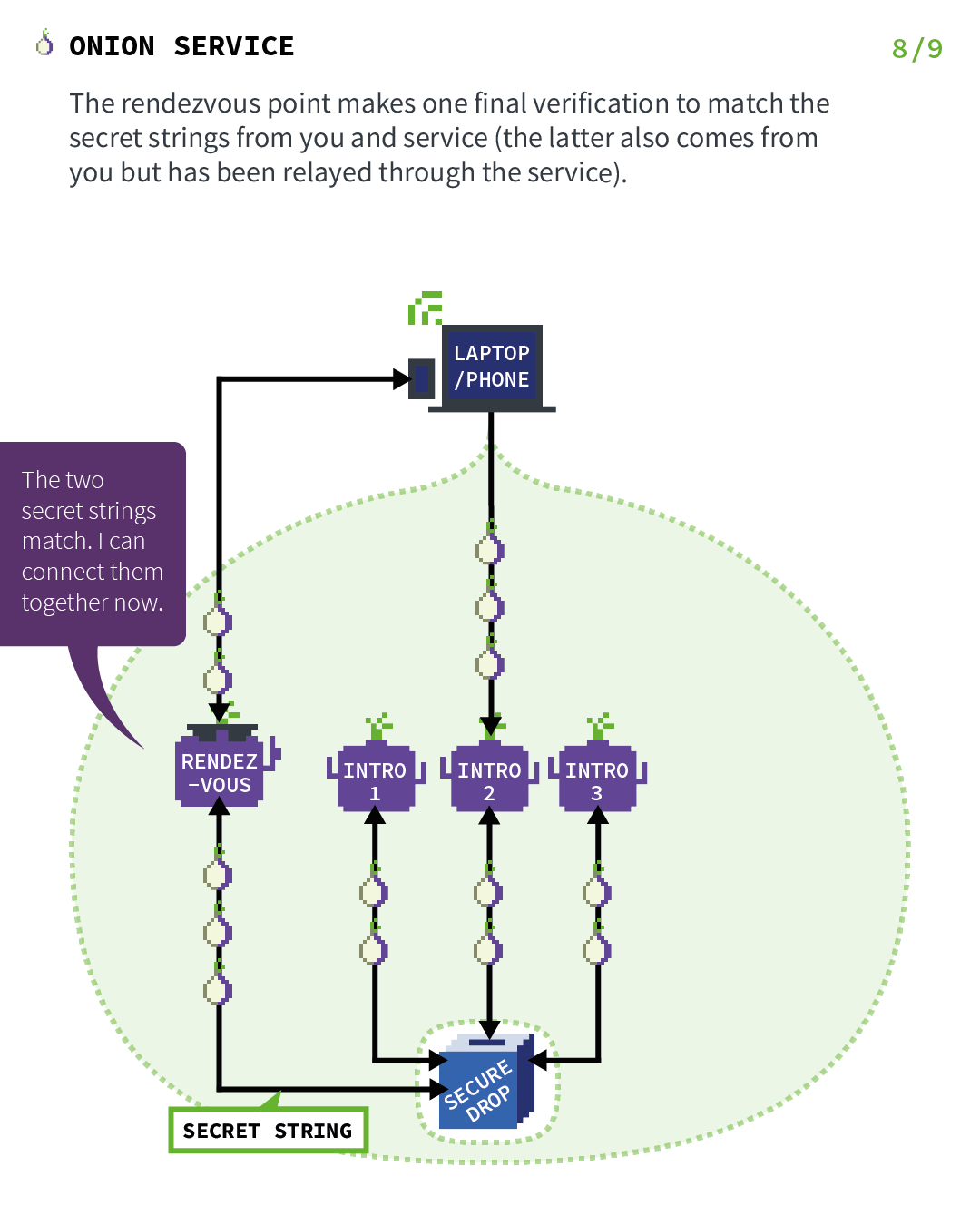
Act 8: Where the rendezvous point verifies the client's secret
Serviciul Onion se conectează la punctul de întâlnire (printr-un circuit anonimizat) și îi trimite „secretul unic”. The rendezvous point makes one final verification to match the secret strings from you and service (the latter also comes from you but has been relayed through the service).
Punctul de întâlnire transmite pur și simplu mesaje (criptate de la un capăt la celălalt) de la client la serviciu și invers.
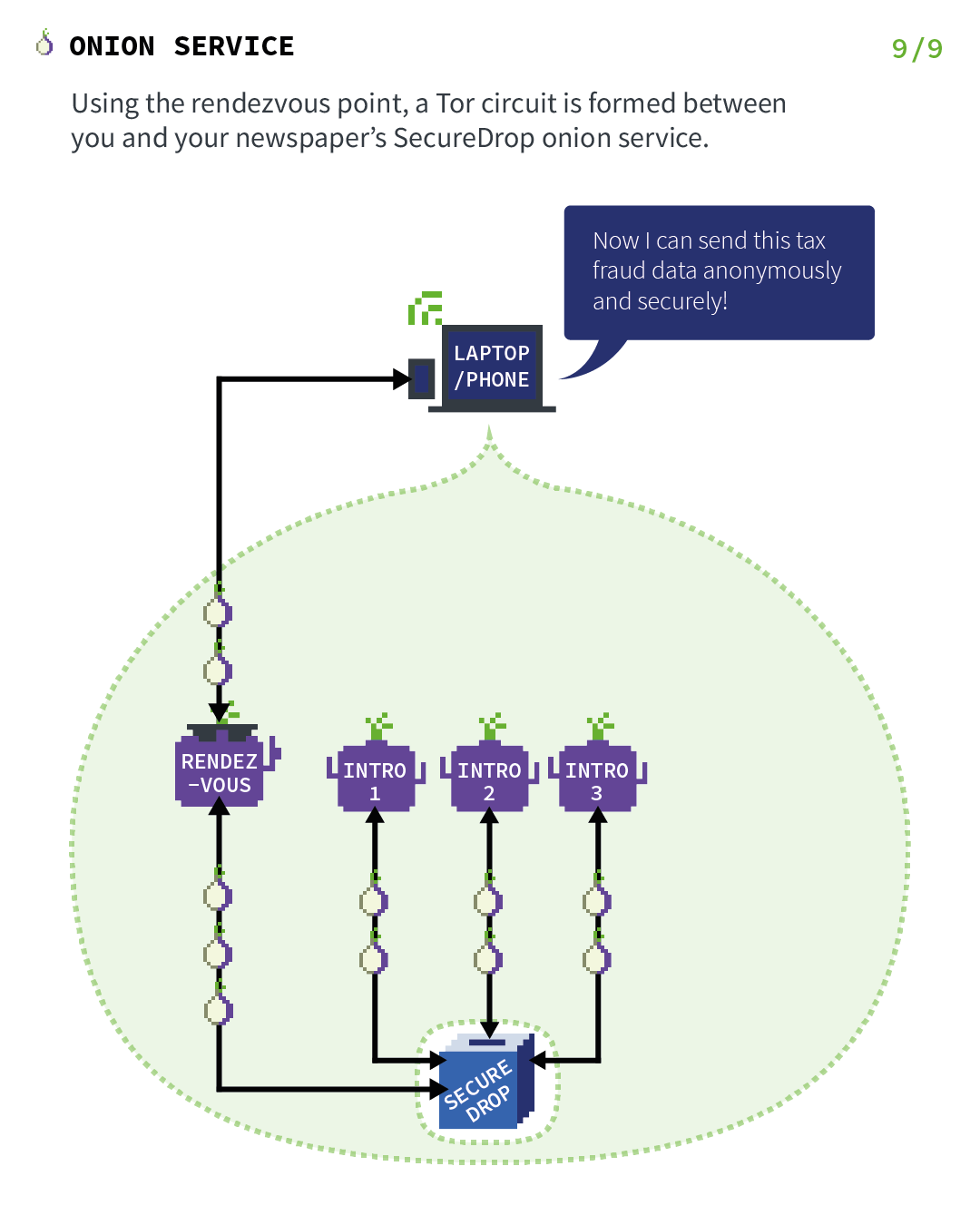
Act 9: Where the onion service rendezvous with the client
In general, the complete connection between client and onion service consists of 6 relays: 3 of them were picked by the client, with the third being the rendezvous point, and the other 3 were picked by the onion service. This provides location hiding to this connection.
Finally, using the rendezvous point, a Tor circuit is formed between you and your newspaper's SecureDrop onion service.
Resurse suplimentare
This was just a high-level overview of the Tor onion services protocol. Here are some more resources if you want to learn more:
- The Tor design paper describing the original design.
- The Tor v3 onion services protocol specification.
- Presentations about onion services: Understanding Tor Onion Services and Their Use Cases - HOPE XI 2016, DEF CON 25 - Roger Dingledine - Next Generation Tor Onion Services.
